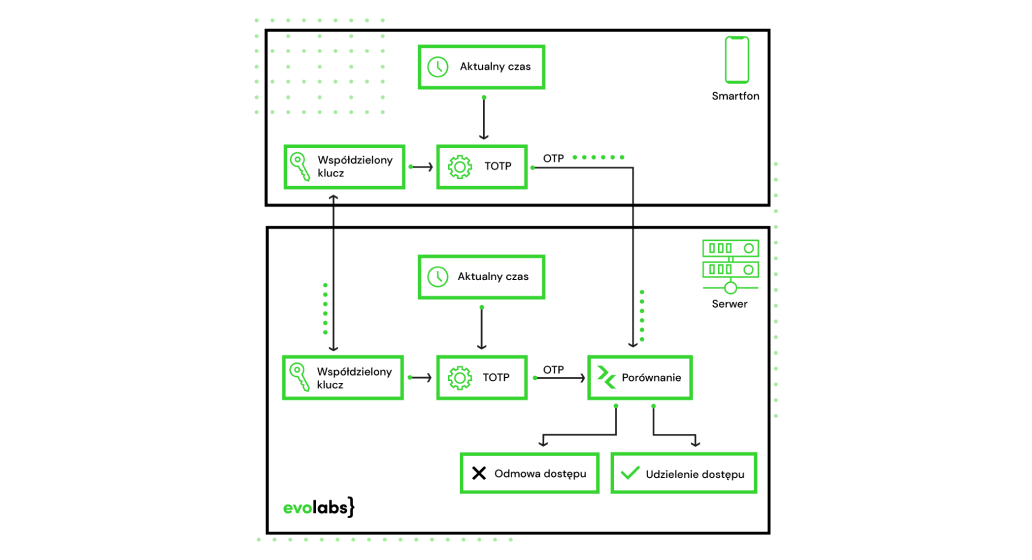
TOTP (Time-Based One-Time Password) is an algorithm that generates one-time passwords based on the current time and a secret key. Due to the uniqueness of these passwords – guaranteed by the use of the current time – this method is widely used in two-factor authentication (2FA). The TOTP algorithm, defined in the RFC 6238 standard (https://datatracker.ietf.org/doc/html/rfc6238), is a time-based version of the HOTP algorithm.
Principle of operation
TOTP, for its operation, requires a unique secret key, shared between the service and the client, and information about the current time (Unix time). The TOTP value is defined as follows:
TOTP = HOTP(K, T)
where K is the shared secret key, and T is an integer value denoting the number of time intervals between the current time and the time from which the intervals are determined. More precisely, the value of T is defined as follows:
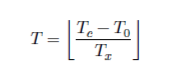
TC ‑ current time (Unix time)
T0 – initial time, from which intervals are determined (usually 0)
Tx – length of the time interval
All times are given in seconds. The determined value is rounded down to an integer value.
For a given time interval Tx (and key), the value generated by the TOTP algorithm is always the same. The previously mentioned RFC 6238 standard recommends a default time step (Tx) value of 30 seconds, which is a balance between security and usability. A larger value extends the time window for a potential attack. In addition, passwords are one-time only, meaning the user would have to wait longer before having another opportunity to enter a password.
The verification service compares the received token with the value generated on the server, taking into account the potential delay introduced by the network.
HOTP (HMAC‑Based One‑Time Password)
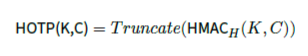
The HOTP algorithm, on which TOTP is based, is defined by the RFC 4226 standard (https://datatracker.ietf.org/doc/html/rfc4226). HOTP generates one-time passwords (OTPs) using HMAC (Keyed-Hashing for Message Authentication) as defined in the RFC 2104 standard (https://datatracker.ietf.org/doc/html/rfc2104).
HOTP is based on a secret key (K), a counter (C) with incremented values, and a cryptographic hash function (H).
The HOTP value is determined as follows:

Security
Resynchronisation
Since TOTP works based on time, and generated passwords are available offline, without a connection between the secured website and the device/application that generates the verified token, we must remember the synchronisation issue.
Currently, the clocks available on devices are characterised by a high constancy in time generation. Nevertheless, in the long term, the difference between the time of the server and the client device may increase. Potential network latency must also be considered. For this reason, the RFC 6238 standard recommends that a password generated for an earlier time interval should also be accepted as correct.
TOTP also defines the ways to resync. For this purpose, the server checks two previous time steps to determine discrepancies between the clocks. The detected difference is stored and considered when the token is re-verified.
Are you going to implement secure two-factor authentication in your SaaS project? Discover the advantages of the TOTP algorithm. Contact us to discuss how we can support your project with advanced security solutions.